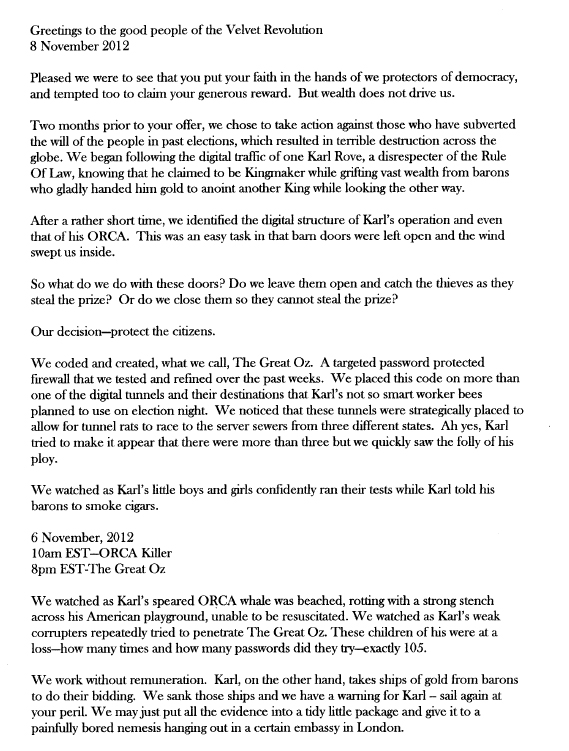
|
| Let's be best friends. You can even come for a sleep over. |
U.S. President Donald Trump invited his Russian counterpart Vladimir Putin to the United States during a phone call, and said he would be glad to see Putin in the White House, RIA Novosti reported on Friday, citing the Russian Foreign Ministry.
The news agency quoted Foreign Minister Sergei Lavrov as saying Trump returned to the subject of an invitation a couple of times during a call last month and that Russia was now expecting Trump to formalize the invitation.
“We proceed from the fact that the U.S. president in a telephone conversation...made such an invitation, said he would be glad to see (Putin) in the White House, would then be glad to meet on a reciprocal visit,” said Lavrov, according to a transcript of an interview with RIA on the foreign ministry website.
“He returned to this topic a couple of times, so we let our American colleagues know that we do not want to impose, but we also do not want to be impolite, and that considering that President Trump made this proposal, we proceed from the position that he will make it concrete.”
Well so much for Trump suddenly getting tough on Putin.
You may remember that trump made this same offer almost exactly a month ago, and for all we know he has made it several times in between.
Of course since then there have been more cyber attacks from Russia, and of course this whole Syria airstrike Kabuki performance.
Let's simply point out once again that Trump is Putin's bitch, and he proves it almost every single day.