Courtesy of the New York Times:
As Russia’s virtual war against the United States continues unabated with the midterm elections approaching, the State Department has yet to spend any of the $120 million it has been allocated since late 2016 to counter foreign efforts to meddle in elections or sow distrust in democracy.
As a result, not one of the 23 analysts working in the department’s Global Engagement Center — which has been tasked with countering Moscow’s disinformation campaign — speaks Russian, and a department hiring freeze has hindered efforts to recruit the computer experts needed to track the Russian efforts.
The delay is just one symptom of the largely passive response to the Russian interference by President Trump, who has made little if any public effort to rally the nation to confront Moscow and defend democratic institutions.
As if you needed ANY more evidence that Donald Trump is a Russian agent.
This also reinforces the New Yorker article about the Kremlin's influence in Trump's decision to choose Rex Tillerson as his Secretary of State.
Just not sure that Mitt Romney would have been so willing to play along with this.
Morality is not determined by the church you attend nor the faith you embrace. It is determined by the quality of your character and the positive impact you have on those you meet along your journey
Showing posts with label computer hacking. Show all posts
Showing posts with label computer hacking. Show all posts
Tuesday, March 06, 2018
Saturday, August 12, 2017
The government has just lost four of its top cyber security officials. Gee, what great timing.
Courtesy of Buzzfeed:
Four senior cybersecurity officials are stepping down from their US government positions, raising concerns that an exodus of top leaders may make the federal government more vulnerable to hacking.
Two of those resigning – Sean Kelley, the chief information security officer for the Environmental Protection Agency, and Richard Staropoli, the chief information officer for the Department of Homeland Security – had been in their jobs for just a few months.
The other two, Rob Foster, the Navy's chief information officer, and Dave DeVries, the director of information security and privacy at the Office of Personnel Management, are departing agencies for which computer security is a top priority. DeVries assumed his job shortly after the OPM suffered the largest known cyberattack in federal government history, and Foster had served in similar positions at the Department of Health and Human Services and Immigration and Customs Enforcement.
Ann Dunkin, the CIO of the EPA under President Barack Obama who was asked to leave by Trump’s transition team and now holds the same title for Santa Clara County, California, told BuzzFeed News that four executives leaving in such a short time raised red flags.
“There appears to be a concerted effort to remove the career CIOs who were there during the Obama administration,” Dunkin said. “During the last week we’ve seen four go? That smells.”
Though the four departing officials gave a variety of reasons for their decision to leave, one source suggested that it was likely due to frustration that multiple key positions within the agency were being left vacant.
This is troubling for one very important reason.
Donald Trump has suggested that Vladimir Putin would not have wanted him to win the election because he plans to build up the military.
But the facts are that Putin could not care less that Trump is wasting taxpayer money on bullets, bombs, and ships.
Putin's latest attack against America could never have been repelled by military aircraft or a regiment of soldiers. To stop those Russian hackers our government needed more highly trained and experienced cyber security experts.
So THIS agency is key to protecting us from the next attempts to hack our government agencies, political parties, or polling stations.
Which should make everybody wonder why increasing the spending and making sure it is fully staffed is not priority one for this administration.
Though sadly once again I think we already know the answer to that question.
Four senior cybersecurity officials are stepping down from their US government positions, raising concerns that an exodus of top leaders may make the federal government more vulnerable to hacking.
Two of those resigning – Sean Kelley, the chief information security officer for the Environmental Protection Agency, and Richard Staropoli, the chief information officer for the Department of Homeland Security – had been in their jobs for just a few months.
The other two, Rob Foster, the Navy's chief information officer, and Dave DeVries, the director of information security and privacy at the Office of Personnel Management, are departing agencies for which computer security is a top priority. DeVries assumed his job shortly after the OPM suffered the largest known cyberattack in federal government history, and Foster had served in similar positions at the Department of Health and Human Services and Immigration and Customs Enforcement.
Ann Dunkin, the CIO of the EPA under President Barack Obama who was asked to leave by Trump’s transition team and now holds the same title for Santa Clara County, California, told BuzzFeed News that four executives leaving in such a short time raised red flags.
“There appears to be a concerted effort to remove the career CIOs who were there during the Obama administration,” Dunkin said. “During the last week we’ve seen four go? That smells.”
Though the four departing officials gave a variety of reasons for their decision to leave, one source suggested that it was likely due to frustration that multiple key positions within the agency were being left vacant.
This is troubling for one very important reason.
Donald Trump has suggested that Vladimir Putin would not have wanted him to win the election because he plans to build up the military.
But the facts are that Putin could not care less that Trump is wasting taxpayer money on bullets, bombs, and ships.
Putin's latest attack against America could never have been repelled by military aircraft or a regiment of soldiers. To stop those Russian hackers our government needed more highly trained and experienced cyber security experts.
So THIS agency is key to protecting us from the next attempts to hack our government agencies, political parties, or polling stations.
Which should make everybody wonder why increasing the spending and making sure it is fully staffed is not priority one for this administration.
Though sadly once again I think we already know the answer to that question.
Labels:
computer hacking,
cyber security,
Donald Trump,
EPA,
hackers,
Trump administration
Monday, July 17, 2017
Vladimir Putin spent a fortune helping Donald Trump get elected, and in many ways was on of his biggest campaign donors.
Courtesy of HuffPo:
The U.S. intelligence community’s Jan. 6 report about Putin’s work to help Trump says the propaganda campaign began with state-paid news organizations like RT and Sputnik.
“RT’s coverage of Secretary Clinton throughout the U.S. presidential campaign was consistently negative and focused on her leaked e-mails and accused her of corruption, poor physical and mental health, and ties to Islamic extremism,” the report states, adding that there was a sophisticated organization to widely distribute that propaganda on the Internet through “professional trolls.”
“The likely financier of the so-called Internet Research Agency of professional trolls located in Saint Petersburg is a close Putin ally with ties to Russian intelligence,” the report says.
Trolls were located in other areas, as well, including Macedonia, where an unusual number of pro-Trump websites were registered.
The number of people involved in the effort is not detailed in the Jan. 6 report, which is an unclassified version of a highly classified assessment. Virginia Sen. Mark Warner, the ranking Democrat on the Senate intelligence committee, in March said there may have been 1,000 such trolls.
If Putin did have that many people working to elect Trump, his operation was more than twice as large as the Trump campaign’s paid staff in the final weeks before the election. And if each Putin cybersoldier was paid just $10,000 over the course of the year, that would put Russia’s expenditure on its pro-Trump propaganda at $10 million, making Putin one of Trump’s biggest financial supporters.
Robert Maguire, with the Center for Responsive Politics, said the situation is similar to rich donors funneling large contributions to secret-money political groups to buy ads.
“The main difference here is that you have a foreign government paying for the creation of stories that get picked up little by little by various news outlets, and in some cases by the candidate himself from the podium,” Maguire said. “Obviously, the aim was to influence, but man, this is so beyond anything we’ve ever seen before. I mean, where do you even start with that?”
It is of course illegal for a foreign government to donate directly to a campaign, or purchase ads on their behalf, but with the creation of fake news stories that were then sent around on social media the Russians found a work around.
And this does not even take into consideration the amount of money and man hours the Russians spent in sending those phishing emails and of course the hacking itself.
Putin does not strike me as the kind of guy who just throws money around without the expectation of a return on his investment.
No, the Russians spent this money in a very targeted way, in order to achieve a very specific payoff.
And that payoff is not simply the election of the most under qualified and idiotic president in American history.
The U.S. intelligence community’s Jan. 6 report about Putin’s work to help Trump says the propaganda campaign began with state-paid news organizations like RT and Sputnik.
“RT’s coverage of Secretary Clinton throughout the U.S. presidential campaign was consistently negative and focused on her leaked e-mails and accused her of corruption, poor physical and mental health, and ties to Islamic extremism,” the report states, adding that there was a sophisticated organization to widely distribute that propaganda on the Internet through “professional trolls.”
“The likely financier of the so-called Internet Research Agency of professional trolls located in Saint Petersburg is a close Putin ally with ties to Russian intelligence,” the report says.
Trolls were located in other areas, as well, including Macedonia, where an unusual number of pro-Trump websites were registered.
The number of people involved in the effort is not detailed in the Jan. 6 report, which is an unclassified version of a highly classified assessment. Virginia Sen. Mark Warner, the ranking Democrat on the Senate intelligence committee, in March said there may have been 1,000 such trolls.
If Putin did have that many people working to elect Trump, his operation was more than twice as large as the Trump campaign’s paid staff in the final weeks before the election. And if each Putin cybersoldier was paid just $10,000 over the course of the year, that would put Russia’s expenditure on its pro-Trump propaganda at $10 million, making Putin one of Trump’s biggest financial supporters.
Robert Maguire, with the Center for Responsive Politics, said the situation is similar to rich donors funneling large contributions to secret-money political groups to buy ads.
“The main difference here is that you have a foreign government paying for the creation of stories that get picked up little by little by various news outlets, and in some cases by the candidate himself from the podium,” Maguire said. “Obviously, the aim was to influence, but man, this is so beyond anything we’ve ever seen before. I mean, where do you even start with that?”
It is of course illegal for a foreign government to donate directly to a campaign, or purchase ads on their behalf, but with the creation of fake news stories that were then sent around on social media the Russians found a work around.
And this does not even take into consideration the amount of money and man hours the Russians spent in sending those phishing emails and of course the hacking itself.
Putin does not strike me as the kind of guy who just throws money around without the expectation of a return on his investment.
No, the Russians spent this money in a very targeted way, in order to achieve a very specific payoff.
And that payoff is not simply the election of the most under qualified and idiotic president in American history.
Labels:
2016,
computer hacking,
election,
fake news,
Huffington Post,
propaganda,
Putin,
Russia,
social media
Sunday, July 09, 2017
One of the largest counties in Texas is returning to paper ballots. A sign of things to come perhaps?
Courtesy of The Texas Tribune:
Frank Phillips spent last Wednesday staring down 600 boxes of election materials — voted ballots, blank ballots, precinct records — sitting in a warehouse run by Denton County. After sitting in storage for the legally required periods — up to nearly two years in some cases — the roughly 24,000 pounds of paper were finally ready to be shredded.
Yet despite the hassle — and the significant cost — Phillips, Denton County’s elections administrator, is looking forward to this fall, when he will implement the county’s newest voting plan: a complete return to the paper ballot.
The unusual move sets Denton, the ninth-largest county in Texas and one of the fastest-growing, apart from the state’s other biggest counties, which all use some form of electronic voting, according to data collected by the Secretary of State’s office. Both Bexar and Harris Counties, for example, have had all electronic voting systems in place for 15 years.
Denton has been using a hybrid voting system that employs both electronic and paper ballots for about a decade. But county officials recently approved spending just shy of $9 million to buy new voting equipment from Austin-based Hart InterCivic that will return to an entirely paper-based system in time for this year's November elections. Even disabled voters, who will cast their votes on touch-screen machines, will have their ballots printed out and tallied through a print scanner.
Ahh, a return to voting system you can trust.
Hopefully the rest of the country will follow suit, especially since we now know that the Russians tried to hack state voter data bases and software systems as well in order to change results.
While we are on the subject of voter suppression, you may like to know that so far only Arkansas has complied with Trump's "Election Integrity" commission and provided all of the voter data that they requested.
So, that is two good news stories about voting integrity in only one post.
Not bad for a Sunday morning.
Frank Phillips spent last Wednesday staring down 600 boxes of election materials — voted ballots, blank ballots, precinct records — sitting in a warehouse run by Denton County. After sitting in storage for the legally required periods — up to nearly two years in some cases — the roughly 24,000 pounds of paper were finally ready to be shredded.
Yet despite the hassle — and the significant cost — Phillips, Denton County’s elections administrator, is looking forward to this fall, when he will implement the county’s newest voting plan: a complete return to the paper ballot.
The unusual move sets Denton, the ninth-largest county in Texas and one of the fastest-growing, apart from the state’s other biggest counties, which all use some form of electronic voting, according to data collected by the Secretary of State’s office. Both Bexar and Harris Counties, for example, have had all electronic voting systems in place for 15 years.
Denton has been using a hybrid voting system that employs both electronic and paper ballots for about a decade. But county officials recently approved spending just shy of $9 million to buy new voting equipment from Austin-based Hart InterCivic that will return to an entirely paper-based system in time for this year's November elections. Even disabled voters, who will cast their votes on touch-screen machines, will have their ballots printed out and tallied through a print scanner.
Ahh, a return to voting system you can trust.
Hopefully the rest of the country will follow suit, especially since we now know that the Russians tried to hack state voter data bases and software systems as well in order to change results.
While we are on the subject of voter suppression, you may like to know that so far only Arkansas has complied with Trump's "Election Integrity" commission and provided all of the voter data that they requested.
So, that is two good news stories about voting integrity in only one post.
Not bad for a Sunday morning.
Labels:
computer hacking,
elections,
integrity,
paper ballots,
Texas,
voting machines
Sunday, January 08, 2017
British intelligence tipped off the US to Russian hacking way back in the fall of 2015. Also tracked communications between Trump advisors and Moscow.
Courtesy of The Guardian:
British intelligence reportedly provided a vital tipoff to the US in 2015 about the extent of Russian hacking on the presidential election.
The report on the UK’s involvement came after US intelligence agencies published an unclassified version of their finding that Vladimir Putin ordered a multi-pronged operation to interfere in the election in favour of Donald Trump.
The New York Times, citing “two people familiar with the conclusions” of the report, said British intelligence was “among the first” to raise the alarm in autumn 2015 that Moscow had hacked the computer servers of the Democratic National Committee.
The Brits also noticed something else:
Over the course the campaign, British officials were as alarmed as their US counterparts over the extent of contacts between Trump advisers and Moscow and by Trump’s consistently pro-Russian stance on a range of foreign policy issues.
Well isn't that interesting? And completely unsurprising?
Here's more:
Allegations about the depth and nature of contacts between the Trump camp and Moscow have been passed to the FBI but it is unclear whether they are the subject of a full investigation.
There was no reference to them in the public version of the joint intelligence report on Russian interference in the election, compiled by the CIA, FBI and NSA.
You know if the FBI can undermine Hillary Clinton's campaign with a last minute, and false, suggestion that she might soon be under criminal indictment, then why are they saying nothing about a possible criminal investigation of Donald Trump before he is sworn into office?
Never mind, I think the answer to that question is because the FBI, or at least director James Comey, may have been compromised in some way.
Which makes me wonder just who else the Russians managed to hack in the lead up to this election?
British intelligence reportedly provided a vital tipoff to the US in 2015 about the extent of Russian hacking on the presidential election.
The report on the UK’s involvement came after US intelligence agencies published an unclassified version of their finding that Vladimir Putin ordered a multi-pronged operation to interfere in the election in favour of Donald Trump.
The New York Times, citing “two people familiar with the conclusions” of the report, said British intelligence was “among the first” to raise the alarm in autumn 2015 that Moscow had hacked the computer servers of the Democratic National Committee.
The Brits also noticed something else:
Over the course the campaign, British officials were as alarmed as their US counterparts over the extent of contacts between Trump advisers and Moscow and by Trump’s consistently pro-Russian stance on a range of foreign policy issues.
Well isn't that interesting? And completely unsurprising?
Here's more:
Allegations about the depth and nature of contacts between the Trump camp and Moscow have been passed to the FBI but it is unclear whether they are the subject of a full investigation.
There was no reference to them in the public version of the joint intelligence report on Russian interference in the election, compiled by the CIA, FBI and NSA.
You know if the FBI can undermine Hillary Clinton's campaign with a last minute, and false, suggestion that she might soon be under criminal indictment, then why are they saying nothing about a possible criminal investigation of Donald Trump before he is sworn into office?
Never mind, I think the answer to that question is because the FBI, or at least director James Comey, may have been compromised in some way.
Which makes me wonder just who else the Russians managed to hack in the lead up to this election?
Labels:
British,
computer hacking,
Donald Trump,
election,
intelligence,
Russians,
The Guardian
Sunday, January 01, 2017
Donald Trump on Russian hacking, "And I also know things that other people don’t know, and so they cannot be sure of the situation."
Courtesy of the New York Times:
Speaking to a handful of reporters outside his Palm Beach, Fla., club, Mar-a-Lago, Mr. Trump cast his declarations of doubt as an effort to seek the truth.
“I just want them to be sure because it’s a pretty serious charge,” Mr. Trump said of the intelligence agencies. “If you look at the weapons of mass destruction, that was a disaster, and they were wrong,” he added, referring to intelligence cited by the George W. Bush administration to support its march to war in 2003. “So I want them to be sure,” the president-elect said. “I think it’s unfair if they don’t know.”
He added: “And I know a lot about hacking. And hacking is a very hard thing to prove. So it could be somebody else. And I also know things that other people don’t know, and so they cannot be sure of the situation.”
When asked what he knew that others did not, Mr. Trump demurred, saying only, “You’ll find out on Tuesday or Wednesday.”
WTF?
So is Trump saying that he has information that the intelligence agencies do not have?
And who gave him this information, his buddy Vlad?
Well then instead of giving him briefings perhaps the intelligence agencies should plop his fat ass in a chair and interrogate him until he gives up his information. After all the integrity of our democracy is as stake here.
Later in the Q and A Trump said this:
“I don’t care what they say, no computer is safe,” he added. “I have a boy who’s 10 years old; he can do anything with a computer. You want something to really go without detection, write it out and have it sent by courier.”
Yes because in the history of mankind nobody has ever murdered or kidnapped a courier to get information, right moron?
So according to Tangerine Hitler he has information that questions the validity of what the intelligence agencies are reporting and thinks all of us should eschew technology and go back to communicating through carrier pigeon.
Good job deplorables! What a great choice you made.
Speaking to a handful of reporters outside his Palm Beach, Fla., club, Mar-a-Lago, Mr. Trump cast his declarations of doubt as an effort to seek the truth.
“I just want them to be sure because it’s a pretty serious charge,” Mr. Trump said of the intelligence agencies. “If you look at the weapons of mass destruction, that was a disaster, and they were wrong,” he added, referring to intelligence cited by the George W. Bush administration to support its march to war in 2003. “So I want them to be sure,” the president-elect said. “I think it’s unfair if they don’t know.”
He added: “And I know a lot about hacking. And hacking is a very hard thing to prove. So it could be somebody else. And I also know things that other people don’t know, and so they cannot be sure of the situation.”
When asked what he knew that others did not, Mr. Trump demurred, saying only, “You’ll find out on Tuesday or Wednesday.”
WTF?
So is Trump saying that he has information that the intelligence agencies do not have?
And who gave him this information, his buddy Vlad?
Well then instead of giving him briefings perhaps the intelligence agencies should plop his fat ass in a chair and interrogate him until he gives up his information. After all the integrity of our democracy is as stake here.
Later in the Q and A Trump said this:
“I don’t care what they say, no computer is safe,” he added. “I have a boy who’s 10 years old; he can do anything with a computer. You want something to really go without detection, write it out and have it sent by courier.”
Yes because in the history of mankind nobody has ever murdered or kidnapped a courier to get information, right moron?
So according to Tangerine Hitler he has information that questions the validity of what the intelligence agencies are reporting and thinks all of us should eschew technology and go back to communicating through carrier pigeon.
Good job deplorables! What a great choice you made.
Labels:
computer hacking,
Donald Trump,
information,
New York Times,
Russians
Sunday, December 18, 2016
Was the FBI's interference in this election a bigger scandal than Watergate?
So the columnist whose tweet is posted above wrote a rather long and expansive examination into what exactly the FBI did to interfere in the 2016 election.Rank-and-file FBI investigators on the Clinton case seem to have said, "If we can't indict her, we'll deny her the presidency." So they did.— Seth Abramson (@SethAbramson) December 14, 2016
You can read the entire thing here, but for the purposes of this post I will concentrate on the twelve most important bullet points:
(1) Abedin told people after the discovery that “she [was] unsure how her emails could have ended up” on the computer the FBI found them on, suggesting that if she’d ever been contacted by the FBI in early October she could have helped them dialogue through the situation (as the idea that she had deliberately withheld these emails from the FBI never made any sense, given the Bureau’s unwavering insistence that Abedin had always been cooperative with them, and the pointlessness of Abedin risking federal Obstruction of Justice charges and federal prison time to hide emails that were—as we now know—not just without any evidentiary value but in fact duplicates of emails she had already turned over to FBI investigators);
(2) consensus in the media and beyond, as summarized by The Washington Post, was that “an announcement from the FBI in early October, when the emails were discovered, might have been less politically damaging for Clinton than one coming less than two weeks before the Nov. 8 election,” a fact no one in the FBI could have failed to appreciate, given its obviousness (even notwithstanding the agents’ enormous, day-to-day professional investment in the situation);
(3) a report in The New York Times indicated that, during the more than three weeks the Weiner investigators kept their discovery from Director Comey, they nevertheless shared their new information with the ”tremendously angry” (see #6, below) rank-and-file FBI investigators from the Clinton email-server case (the New York Times having reported on October 30th that the discovery of “new” Abedin emails in early October “prompted a renewed interest among agents who had investigated Mrs. Clinton for her use of a private email server as Secretary of State” [emphasis supplied]);
(4) after the late-October revelation that the FBI had found new emails on Weiner’s computer on October 3rd, rank-and-file FBI agents told the media that “there was no chance the email review could be completed before Election Day” (thus ensuring it would disrupt the Clinton campaign through the casting of all ballots, early and in-person), only to be overruled by Director Comey within 24 hours, with Comey decreeing that the relevance of the new emails would be determined by Election Day (as it ultimately was, after many millions of Americans had voted early, and before many more millions could hear about the second, exculpatory Comey letter; nevertheless, the stark disparity between the rank-and-file’s comments to the media and Comey’s comments remains unexplained);
(5) a member of Trump’s inner circle, Rudy Giuliani, confessed on the Lars Larson radio program that current FBI agents working on the Clinton investigation had illegally leaked information to him about the Abedin emails before it became public and before Director Comey had been told of the emails, and, moreover, were intending to leak this information—if they were unable to get Comey to do it via the implicit threat of a leak—as an (in Giuliani’s words) pro-Trump “October Surprise,” thereby establishing a political motive among a faction of the FBI in the timing and dissemination of information about the emails (”Darn right I heard about it,” said Giuliani, “[and] I can’t even repeat the language I heard,” referring with this latter remark to the agents’ anger at not being able to indict Hillary Clinton for multiple federal felonies in July of 2016; concurrently, Jim Kallstrom, who headed the New York field office of the FBI in the 1990s, also admitted to Fox News to receiving leaks about the Clinton investigation from current FBI agents working on the case);
(6) Giuliani further disclosed that a faction of rank-and-file FBI agents within the New York field office felt “tremendous anger” toward both Director Comey, Hillary Clinton (the subject of their investigation, who they believed should have been indicted in July), and “a pretty corrupt Obama Justice Department” (many of whose officials might have retained their posts if Clinton were to win election to the presidency), and we know from The Chicago Tribune that Comey wrote “the Comey Letter” only because he believed these same rogue FBI agents in New York were planning to leak the “new” evidence in the Weiner case (which leak would have violated numerous federal criminal statutes, and which plan to leak would already be regarded as a criminal conspiracy by law);
(7) the Abedin emails turned out to have no evidentiary value, and indeed were in many instances duplicates of emails already held by the FBI, which fact Comey likely could have determined himself even from meta-data alone (had he been given the opportunity to do so during the first week of October);
(8) Giuliani mysteriously took himself out of the running for any position within the Trump administration on the very same day (December 9th) that The Washington Post and The New York Times ran stories about Russian interference with the 2016 presidential election, thereby beginning a period of heavy scrutiny for both the FBI and CIA’s actions before and during the election, with the stated reason for Giuliani’s demurral from a once-certain Cabinet position being his potential conflicts of interest abroad (which conflicts are reportedly far fewer in number than those of either the President-elect or the President-elect’s nominee for Secretary of State, and occur in the context of an administration that has thus far expressed no concern at all about foreign business entanglements);
(9) as reported by The Chicago Tribune, a Los Angeles attorney, E. Randol Schoenberg, is now asking a New York City judge to release, on Thursday, the search warrant the FBI sought for the Abedin emails on Weiner’s computer—with what probable cause to believe they contained evidence of criminal conduct one can, in view of the facts in this article, only begin to imagine—with Schoenberg’s stated purpose being to determine whether “someone in the Manhattan orbit of then-candidate Donald Trump may have provided a false lead to the FBI” regarding the Abedin emails (alternatively, as observed by The Gothamist, the search warrant could turn up “funny business by overly zealous conservative FBI agents”);
(10) the lawsuit in New York was made necessary by the FBI’s inexplicable refusal to turn over its FOIA-eligible investigatory materials to Attorney Schoenberg in the 20-day window mandated by law, or even to respond to Schoenberg’s request at all, which refusal would have assured, absent Schoenberg’s lawsuit, that this information would remain under wraps prior to the Electoral College vote;
(11) the judge in the New York lawsuit now says he may release the entirety of the search warrant prior to the meeting of the Electoral College on Monday, December 19th, acknowledging thereby the potential political relevance of the material; and
(12) if the search warrant is in any way irregular, or the FBI’s redactions from it suspicious, this could confirm political collusion at the FBI and thereby increase the number of “Hamilton Electors” from their current reported 20 to the 38 needed to throw the 2016 presidential election to the House of Representatives—which temporary delay in Trump’s ascension to the presidency would allow ample time for investigations of both FBI collusion with the Trump campaign and multifaceted Russian interference with the presidential election.
There is actually a lot more in the post, but these points alone are more than enough to suggest, if not prove, that there was a definite conspiracy to deny Hillary Clinton the presidency.
Then add to that the Republican witch hunts over Benghazi and the private server, Russian hacking, and voting irregularities, and there simply is no longer any doubt.
In my opinion Watergate was child's play compared to this, and what is even more troubling is that it is about to be swept under the rug by a media that is desperate to maintain access to the new president at the expense of reporting the most egregious attack on our democracy perhaps in our entire 240 year history.
Labels:
computer hacking,
conspiracy,
Donald Trump,
e-mails,
election,
FBI,
Hillary Clinton,
James Comey,
letter,
Watergate
Saturday, September 24, 2016
Top Democrats finally proclaim publicly that the Russian government is trying to sway this election. No, really?
Courtesy of Politico:
The top Democrats on the House and Senate Intelligence panels said Thursday that they are convinced, based on briefings, that senior Russian officials are trying to sway or disrupt the U.S. elections.
"Based on briefings we have received, we have concluded that the Russian intelligence agencies are making a serious and concerted effort to influence the U.S. election," said Sen. Dianne Feinstein and Rep. Adam Schiff in a joint statement.
"At the least, this effort is intended to sow doubt about the security of our election and may well be intended to influence the outcomes of the election - we can see no other rationale for the behavior of the Russians," they added.
The pair placed the blame at the highest levels of Russia's government.
"We believe that orders for the Russian intelligence agencies to conduct such actions could come only from very senior levels of the Russian government," they said.
This does not exactly come as news to those of us paying attention to all of these hacks, and the fact that they seem focused mostly on the Democrats and opponents of Donald Trump.
Speaking of Trump, it appears that one of his advisors is under investigation for his dealings with Russia:
One of Donald Trump's foreign policy advisors is being probed by U.S. intelligence officials to determine whether he has had private discussions with senior Russian officials, Yahoo News reported, citing sources. In particular, members of the intelligence community are concerned that Carter Page has spoken with the Kremlin about the possibility of lifting economic sanctions on Russia, sources told Yahoo.
The former Soviet Union working to help a Republican win a presidential election. I wonder if you can die from an irony overload?
The top Democrats on the House and Senate Intelligence panels said Thursday that they are convinced, based on briefings, that senior Russian officials are trying to sway or disrupt the U.S. elections.
"Based on briefings we have received, we have concluded that the Russian intelligence agencies are making a serious and concerted effort to influence the U.S. election," said Sen. Dianne Feinstein and Rep. Adam Schiff in a joint statement.
"At the least, this effort is intended to sow doubt about the security of our election and may well be intended to influence the outcomes of the election - we can see no other rationale for the behavior of the Russians," they added.
The pair placed the blame at the highest levels of Russia's government.
"We believe that orders for the Russian intelligence agencies to conduct such actions could come only from very senior levels of the Russian government," they said.
This does not exactly come as news to those of us paying attention to all of these hacks, and the fact that they seem focused mostly on the Democrats and opponents of Donald Trump.
Speaking of Trump, it appears that one of his advisors is under investigation for his dealings with Russia:
One of Donald Trump's foreign policy advisors is being probed by U.S. intelligence officials to determine whether he has had private discussions with senior Russian officials, Yahoo News reported, citing sources. In particular, members of the intelligence community are concerned that Carter Page has spoken with the Kremlin about the possibility of lifting economic sanctions on Russia, sources told Yahoo.
The former Soviet Union working to help a Republican win a presidential election. I wonder if you can die from an irony overload?
Labels:
computer hacking,
Democrats,
Dianne Feinstein,
Donald Trump,
election,
interference,
politics,
Putin,
Russia
Thursday, May 05, 2016
Romanian hacker claims to have hacked into Hillary Clinton's e-mail server, but did he?
So the internet is abuzz with news about his "Guccifer" fellow who now claims that he used Sydney Blumenthal's e-mail account, after guessing his password, to hack into Clinton's account as well.
There are a couple of red flags that his story might be pure BS, but Fox News is fairly convinced:
EXCLUSIVE: The infamous Romanian hacker known as “Guccifer,” speaking exclusively with Fox News, claimed he easily – and repeatedly – breached former Secretary of State Hillary Clinton’s personal email server in early 2013.
"For me, it was easy ... easy for me, for everybody," Marcel Lehel Lazar, who goes by the moniker "Guccifer," told Fox News from a Virginia jail where he is being held.
Guccifer’s potential role in the Clinton email investigation was first reported by Fox News last month. The hacker subsequently claimed he was able to access the server – and provided extensive details about how he did it and what he found – over the course of a half-hour jailhouse interview and a series of recorded phone calls with Fox News.
Fox News leaves a little wiggle room in case this guy, Marcel Lehel Lazar, turns out to be yanking their chain, but you can sense their excitement in the almost breathless way they are reporting this. Also making damn sure that everybody knows that THEY had the story first.
Except of course they didn't.
NBC had already interviewed this individual, who is serving a four year sentence for his crimes which include hacking into the Bush family e-mail accounts, before he was extradited.
Here is how NBC reported the story today:
When pressed by NBC News, Lazar, 44, could provide no documentation to back up his claims, nor did he ever release anything online supporting his allegations, as he had frequently done with past hacks. The FBI's review of the Clinton server logs showed no sign of hacking, according to a source familiar with the case.
Brian Fallon, national press secretary for Clinton's presidential campaign, said Guccifer's claims were baseless.
"There is absolutely no basis to believe the claims made by this criminal from his prison cell," said Fallon. "In addition to the fact that he offers no proof to support his claims, his descriptions of Secretary Clinton's server are inaccurate. It is unfathomable that he would have gained access to her emails and not leaked them the way he did to his other victims.
"We have received no indication from any government agency to support these claims, nor are they reflected in the range of charges that Guccifer already faces and that prompted his extradition in the first place," Fallon added. "And it has been reported that security logs from Secretary Clinton's email server do not show any evidence of foreign hacking."
Apparently this Lazar fellow also claimed that there was nothing interesting in the e-mails, but then in other reports that he saved data, which obviously he never used.
So right now the Right Wing blogs, and of course Bernie supporters, are losing their minds over this and claiming that it proves Clinton is doomed.
However the first thing to remember is that there is still no evidence that this even happened. Secondly, if it did, that the State Department e-mail system was ALSO hacked. And thirdly that it is incredibly unlikely that this will have any effect whatsoever on Hillary's campaign in the real world.
Labels:
campaign,
computer hacking,
e-mails,
FBI,
Hillary Clinton,
investigation,
politics
Thursday, February 27, 2014
Chinese cyber attacks and how Edward Snowden became their not so secret weapon.
Courtesy of the New York Post:
China’s military hackers are back, more brazen than ever. You can thank Edward Snowden.
A year ago, the Internet security firm Mandiant went public with what cyber-war watchers had known for some time: Unit 61398, a secret branch of the Chinese military, had been behind more than 1,000 cyber attacks on Western targets since 2006. Employing thousands of trained cyber warriors housed in a 12-story building in Shanghai — and backed by an enormous militia of part-time hackers — Unit 61398 had been waging a constant war on foreign banks, infrastructure, defense firms and government agencies, including one spectacular 2007 raid on the Pentagon that shut down 1,500 different Defense Department networks.
The resulting international sensation forced a reluctant President Obama to confront the Chinese premier on the issue. Beijing issued its usual furious denial — but the attacks stopped and Unit 61398 fell from the headlines.
But now we know they didn’t stop for long — and the West and the Obama administration are looking as ill-prepared and impotent as ever in dealing with the threat. China’s usual attacks on banks, weapons manufacturers and other juicy targets are now back to almost daily.
The first big attack came as early as late May, when Chinese hackers raided networks at top US defense firms, swiping information on more than two dozen weapons systems.
In October, they hit the Federal Electoral Commission, suggesting the People’s Liberation Army is looking at ways to interfere in the US electoral process.
In December, they launched a series of attacks on the foreign ministries of five countries ahead of the G-20 summit, using an infected e-mail attachment that was supposed to provide updates on the Syria crisis. (Not as clever as Unit 61398’s similar 2011 attack, which used an e-mail promising nude photos of then French President Nicholas Sarkozy’s wife, Carla Bruni.)
The latest outrage came Feb. 11, when evidence revealed Chinese cyber warriors had cracked open the Veterans of Foreign Wars computer system — itself not an obvious security threat, but part of what experts believe was a much broader attack on US military personnel records and files, both past and current.
Most striking is how bold the attacks have grown. The Chinese are apparently so confident we can’t (or won’t) stop them that they’ve gotten sloppy. Examining hacker codes left behind on US military and commercial networks, Internet-security engineers have been finding bits of code identical to Chinese commercial software sold for export by companies with contracts with the People’s Liberation Army.
What has emboldened the Chinese military hackers?
Well that would be Edward Snowden.
The Snowden defection back in June was a double gift for China’s hackers (as well as for Russian ones — the State Department even issued a warning that any cellphone or laptop brought to the Sochi Olympics would almost certainly be hacked there, and its passwords stolen).
The data Snowden brought with him to Hong Kong included a wealth of information about how our intelligence agencies fight and trace hackers, as well as on the NSA’s own hacking efforts in China.
Not only has the information that Snowden carried into China given them the blueprint for how our data gathering system work, but the fact that we have data gathering systems has allowed China, who hacks into American businesses to sell the information to Chinese businesses, to play the moral equivalency game.
If the US does it, how can they point the finger at us?
Here is more from a Newsweek article from November:
"Snowden couldn't have played better into China's strategy for protecting its cyber activities if he had been doing it on purpose,'' one American intelligence official says.
Snowden's revelations quickly veered away from what he called the NSA's "domestic surveillance state" to overseas espionage by the United States. After fleeing to Hong Kong, he provided local reporters with NSA documents and told them the United States was hacking major Chinese telecommunications companies, a Beijing university and the corporate owner of the region's most extensive fiber-optic submarine cable network. That information, government officials and industry experts say, is now used by the Chinese to deflect criticisms of their hacking, both in meetings with the administration and at cyber security conferences.
The activities of the two sides, however, are vastly different in scope and intent. The United States engages in widespread electronic espionage, but that classified information cannot legally be handed over to private industry. China is using its surveillance to steal trade secrets, harm international competitors and undermine American businesses.
In Snowden's zeal to be the next Daniel Ellsberg he has instead become perhaps the worst American traitor since Aldrich Ames.
If Snowden had released his information to journalists here in the country, and kept the stolen data within American borders, he could rightfully be called a hero.
But taking such sensitive material out of the country, and reporting on our data gathering process to nations with an adversarial relationship with America, Snowden has not only placed our state secrets in jeopardy, he has also irrevocably damaged out ability to deal with cyber attacks, or hold those who do them accountable.
China’s military hackers are back, more brazen than ever. You can thank Edward Snowden.
A year ago, the Internet security firm Mandiant went public with what cyber-war watchers had known for some time: Unit 61398, a secret branch of the Chinese military, had been behind more than 1,000 cyber attacks on Western targets since 2006. Employing thousands of trained cyber warriors housed in a 12-story building in Shanghai — and backed by an enormous militia of part-time hackers — Unit 61398 had been waging a constant war on foreign banks, infrastructure, defense firms and government agencies, including one spectacular 2007 raid on the Pentagon that shut down 1,500 different Defense Department networks.
The resulting international sensation forced a reluctant President Obama to confront the Chinese premier on the issue. Beijing issued its usual furious denial — but the attacks stopped and Unit 61398 fell from the headlines.
But now we know they didn’t stop for long — and the West and the Obama administration are looking as ill-prepared and impotent as ever in dealing with the threat. China’s usual attacks on banks, weapons manufacturers and other juicy targets are now back to almost daily.
The first big attack came as early as late May, when Chinese hackers raided networks at top US defense firms, swiping information on more than two dozen weapons systems.
In October, they hit the Federal Electoral Commission, suggesting the People’s Liberation Army is looking at ways to interfere in the US electoral process.
In December, they launched a series of attacks on the foreign ministries of five countries ahead of the G-20 summit, using an infected e-mail attachment that was supposed to provide updates on the Syria crisis. (Not as clever as Unit 61398’s similar 2011 attack, which used an e-mail promising nude photos of then French President Nicholas Sarkozy’s wife, Carla Bruni.)
The latest outrage came Feb. 11, when evidence revealed Chinese cyber warriors had cracked open the Veterans of Foreign Wars computer system — itself not an obvious security threat, but part of what experts believe was a much broader attack on US military personnel records and files, both past and current.
Most striking is how bold the attacks have grown. The Chinese are apparently so confident we can’t (or won’t) stop them that they’ve gotten sloppy. Examining hacker codes left behind on US military and commercial networks, Internet-security engineers have been finding bits of code identical to Chinese commercial software sold for export by companies with contracts with the People’s Liberation Army.
What has emboldened the Chinese military hackers?
Well that would be Edward Snowden.
The Snowden defection back in June was a double gift for China’s hackers (as well as for Russian ones — the State Department even issued a warning that any cellphone or laptop brought to the Sochi Olympics would almost certainly be hacked there, and its passwords stolen).
The data Snowden brought with him to Hong Kong included a wealth of information about how our intelligence agencies fight and trace hackers, as well as on the NSA’s own hacking efforts in China.
Not only has the information that Snowden carried into China given them the blueprint for how our data gathering system work, but the fact that we have data gathering systems has allowed China, who hacks into American businesses to sell the information to Chinese businesses, to play the moral equivalency game.
If the US does it, how can they point the finger at us?
Here is more from a Newsweek article from November:
"Snowden couldn't have played better into China's strategy for protecting its cyber activities if he had been doing it on purpose,'' one American intelligence official says.
Snowden's revelations quickly veered away from what he called the NSA's "domestic surveillance state" to overseas espionage by the United States. After fleeing to Hong Kong, he provided local reporters with NSA documents and told them the United States was hacking major Chinese telecommunications companies, a Beijing university and the corporate owner of the region's most extensive fiber-optic submarine cable network. That information, government officials and industry experts say, is now used by the Chinese to deflect criticisms of their hacking, both in meetings with the administration and at cyber security conferences.
The activities of the two sides, however, are vastly different in scope and intent. The United States engages in widespread electronic espionage, but that classified information cannot legally be handed over to private industry. China is using its surveillance to steal trade secrets, harm international competitors and undermine American businesses.
In Snowden's zeal to be the next Daniel Ellsberg he has instead become perhaps the worst American traitor since Aldrich Ames.
If Snowden had released his information to journalists here in the country, and kept the stolen data within American borders, he could rightfully be called a hero.
But taking such sensitive material out of the country, and reporting on our data gathering process to nations with an adversarial relationship with America, Snowden has not only placed our state secrets in jeopardy, he has also irrevocably damaged out ability to deal with cyber attacks, or hold those who do them accountable.
Labels:
China,
computer hacking,
cyber attacks,
Edward Snowden,
New York Post,
Newsweek,
NSA
Wednesday, July 17, 2013
Edward Snowden claims that he is torture proof and that his information cannot be hacked. Somewhere there is an uncharacteristic smile creeping across the face of Vladimir Putin.
 |
| Cannot be tortured into talking you say? |
The dramatic plot of the Edward Snowden NSA whistleblowing saga has just taken an interesting twist: in a letter to U.S. Senator Gordon Humphreys, Snowden declares himself impervious to torture.
Furthermore, he claims his encryption cannot be hacked.
From his letter, posted in the Guardian:
[N]o intelligence service — not even our own — has the capacity to compromise the secrets I continue to protect. While it has not been reported in the media, one of my specializations was to teach our people at DIA how to keep such information from being compromised even in the highest threat counter-intelligence environments (i.e. China).
You may rest easy knowing I cannot be coerced into revealing that information, even under torture.
You know the idea of saying something like this, while sitting in Russia, under the watchful of ex-KGB agent Vladimir Putin, seems the very definition of insanity.
If Putin WANTS to see what Snowden has, assuming he has not already seen it,then he WILL see what Snowden has. Period!
If Snowden thinks that Putin is on his side, or shares his vision of respecting the rights of people not to be spied on by their government, then he is a bigger fool than any of us may have thought.
What's more, if Snowden is granted asylum by the Russian government his trouble may have only just begun.
Labels:
asylum,
computer hacking,
Edward Snowden,
NSA,
Russia,
spies,
torture
Saturday, November 17, 2012
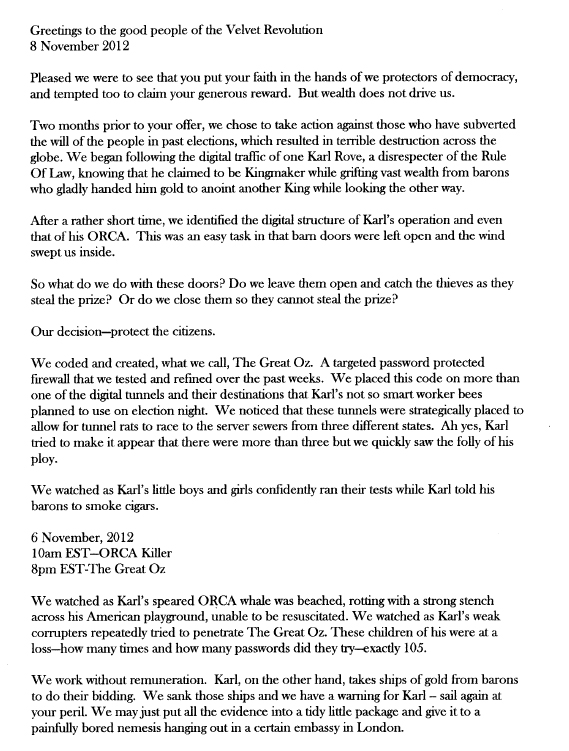
Did the secret cyber justice group "Anonymous" prevent Karl Rove from stealing the 2012 election? According to them they did. Update!
A few weeks before the election this video was posted on YouTube:
At the time I think many of us took the group's ability to affect the outcome of the election with a grain of salt, even though I think the majority of us also believed that Rove did DID indeed have a plot to steal it away from the President.
Later of course we all witnessed Karl Rove's breakdown on live TV as he slowly came to the realization that SOMETHING had gone awry.
However now Anonymous is stating for a fact that the fix was mostly definitely in, and that THEY were both the reason it did not work, AND the reason for Rove's televised tantrum.
Here is their statement in full:
Now I have no way of checking as to whether this group did what they said they did, but the fact that SOMETHING went wrong with Rove's ORCA program was confirmed in an article for the Atlantic about Obama's "Dream Team" of nerds:
The billing the Republicans gave the tool confused almost everyone inside the Obama campaign. Narwhal wasn't an app for a smartphone. It was the architecture of the company's sophisticated data operation. Narwhal unified what Obama for America knew about voters, canvassers, event-goers, and phone-bankers, and it did it in real time. From the descriptions of the Romney camp's software that were available then and now, Orca was not even in the same category as Narwhal. It was like touting the iPad as a Facebook killer, or comparing a GPS device to an engine. And besides, in the scheme of a campaign, a digitized strike list is cool, but it's not, like, a gamechanger. It's just a nice thing to have.
So, it was with more than a hint of schadenfreude that Reed's team hear(d) that Orca crashed early on election day. Later reports posted by rank-and-file volunteers describe chaos descending on the polling locations as only a fraction of the tens of thousands of volunteers organized for the effort were able to use it properly to turn out the vote.
So I will leave it to you to determine whether Anonymous is actually behind Rove's failure, or whether it was simply buried under the weight of high voter turnout for Democrats, or whether Obama's team of nerds simply outsmarted Turdblossom.
However I will say that if Anonymous is being honest, and they DID manage to sabotage this cyber attack on democracy, then I feel they need to immediately share their information with the Justice department, the Democratic party, and the American press. Because if they are right, then our elections are still incredibly vulnerable to this kind of hacking and that needs to be addressed and dealt with just as soon as possible.
Oh and Karl Rove needs to grabbed off the street and thrown into the darkest, coldest, most inhospitable jail cell in this, or any other, country, until his trial for treason. After which I expect to see his bullet riddled carcass dragged through the streets as a warning to ANYBODY who wants to impinge on the rights of America's voters to choose their leaders fairly.
Update: It looks as if Thom Hartmann is pretty convinced that Anonymous did indeed stop Karl Rove.
At the time I think many of us took the group's ability to affect the outcome of the election with a grain of salt, even though I think the majority of us also believed that Rove did DID indeed have a plot to steal it away from the President.
Later of course we all witnessed Karl Rove's breakdown on live TV as he slowly came to the realization that SOMETHING had gone awry.
However now Anonymous is stating for a fact that the fix was mostly definitely in, and that THEY were both the reason it did not work, AND the reason for Rove's televised tantrum.
Here is their statement in full:
 |
| Click for PDF. |
The billing the Republicans gave the tool confused almost everyone inside the Obama campaign. Narwhal wasn't an app for a smartphone. It was the architecture of the company's sophisticated data operation. Narwhal unified what Obama for America knew about voters, canvassers, event-goers, and phone-bankers, and it did it in real time. From the descriptions of the Romney camp's software that were available then and now, Orca was not even in the same category as Narwhal. It was like touting the iPad as a Facebook killer, or comparing a GPS device to an engine. And besides, in the scheme of a campaign, a digitized strike list is cool, but it's not, like, a gamechanger. It's just a nice thing to have.
So, it was with more than a hint of schadenfreude that Reed's team hear(d) that Orca crashed early on election day. Later reports posted by rank-and-file volunteers describe chaos descending on the polling locations as only a fraction of the tens of thousands of volunteers organized for the effort were able to use it properly to turn out the vote.
So I will leave it to you to determine whether Anonymous is actually behind Rove's failure, or whether it was simply buried under the weight of high voter turnout for Democrats, or whether Obama's team of nerds simply outsmarted Turdblossom.
However I will say that if Anonymous is being honest, and they DID manage to sabotage this cyber attack on democracy, then I feel they need to immediately share their information with the Justice department, the Democratic party, and the American press. Because if they are right, then our elections are still incredibly vulnerable to this kind of hacking and that needs to be addressed and dealt with just as soon as possible.
Oh and Karl Rove needs to grabbed off the street and thrown into the darkest, coldest, most inhospitable jail cell in this, or any other, country, until his trial for treason. After which I expect to see his bullet riddled carcass dragged through the streets as a warning to ANYBODY who wants to impinge on the rights of America's voters to choose their leaders fairly.
Update: It looks as if Thom Hartmann is pretty convinced that Anonymous did indeed stop Karl Rove.
Friday, November 04, 2011
There is a storm brewing for Fox News this weekend. Time to batten down the hatches Rupert.
I have to say that I am pretty jazzed about this.
If these folks can bring down Fox News they will go down in history as American patriots.
By the way, is anybody else planning to celebrate the fifth by watching "V for Vendetta?"
If these folks can bring down Fox News they will go down in history as American patriots.
By the way, is anybody else planning to celebrate the fifth by watching "V for Vendetta?"
Labels:
anonymous,
computer hacking,
FOX News,
journalism,
justice
Friday, September 23, 2011
Joe McGinniss responds to leaked e-mail.
It looks like Joe responded to Mediaite concerning the e-mail:
My email to Jesse Griffin was an effort to secure Alaskan help in obtaining further corroboration of allegations about Sarah Palin that came to my attention during my research. My reporting continued beyond the date of the email, and only information that checked out to my satisfaction and that of my publisher was included in the book. Ultimately, I published only those allegations which I found to be credible. Other allegations that could not be sufficiently verified, including some of those referenced in my email, are not in my book.
Yes that is precisely correct.
As I mentioned earlier Joe had contacted me after leaving Alaska and asked me try and convince some more sources to go on the record. This is what I wrote about that exchange:
Even after Joe left Alaska he said "Jesse I need something more than what I found up there." So I tried some more, and essentially ran off people who had once claimed repeatedly to be willing to talk to "the right journalist or author." (If freaking Joe McGinniss was not "the right author" who in the hell were they waiting to interview them?)
I think I was only able to help him with one or two of his questions, but the point was that he was asking if anybody could verify these stories, NOT that he wanted to hear more rumors. (Some like the Brad Hanson affair, I knew less than he did about. Though I DID speak to the reporter that broke the story. And at least three people in Wasilla that also knew of it. Joe knows them as well.)
However the majority of Joe's book is from eyewitness sources that saw the things reported happen just as he describes them. And I certainly did not connect him with Glen Rice, who has substantiated his tryst with Sister Sarah and has no problem with how it is described in the book.
For those taken aback by Joe's style in the e-mail all I have to say is THAT is how Joe talks. There is no patience for bullshit, and he does not beat around the bush.
And do you know what? I was not offended or bothered one little bit, because I knew that the standards for writing a book (And the legal scrutiny that it is subjected to), were MUCH different for a book than they are for my blog. Which is obviously quite an understatement.
Yes the Right Wing will use this, and every thing else they can find, in a desperate attempt to discredit this book. But hey if it keeps selling than they fail don't they?
And let's face it, WHO among the viewers of Fox News, and the visitors to Breitbat's blog, were going to buy it anyhow?
The MUCH more important question in my mind is HOW did Breitbart get that e-mail?
I don't share my private e-mails with ANYBODY! At least on my end, the only two people who should have seen it are Joe and I. And really WHY would Joe send it to anybody else?
So is it possible that we now have an American case of News Corp phone hacking techniques being used by a well known contributor to Fox News? That is the question that I want to see answered!
My email to Jesse Griffin was an effort to secure Alaskan help in obtaining further corroboration of allegations about Sarah Palin that came to my attention during my research. My reporting continued beyond the date of the email, and only information that checked out to my satisfaction and that of my publisher was included in the book. Ultimately, I published only those allegations which I found to be credible. Other allegations that could not be sufficiently verified, including some of those referenced in my email, are not in my book.
Yes that is precisely correct.
As I mentioned earlier Joe had contacted me after leaving Alaska and asked me try and convince some more sources to go on the record. This is what I wrote about that exchange:
Even after Joe left Alaska he said "Jesse I need something more than what I found up there." So I tried some more, and essentially ran off people who had once claimed repeatedly to be willing to talk to "the right journalist or author." (If freaking Joe McGinniss was not "the right author" who in the hell were they waiting to interview them?)
I think I was only able to help him with one or two of his questions, but the point was that he was asking if anybody could verify these stories, NOT that he wanted to hear more rumors. (Some like the Brad Hanson affair, I knew less than he did about. Though I DID speak to the reporter that broke the story. And at least three people in Wasilla that also knew of it. Joe knows them as well.)
However the majority of Joe's book is from eyewitness sources that saw the things reported happen just as he describes them. And I certainly did not connect him with Glen Rice, who has substantiated his tryst with Sister Sarah and has no problem with how it is described in the book.
For those taken aback by Joe's style in the e-mail all I have to say is THAT is how Joe talks. There is no patience for bullshit, and he does not beat around the bush.
And do you know what? I was not offended or bothered one little bit, because I knew that the standards for writing a book (And the legal scrutiny that it is subjected to), were MUCH different for a book than they are for my blog. Which is obviously quite an understatement.
Yes the Right Wing will use this, and every thing else they can find, in a desperate attempt to discredit this book. But hey if it keeps selling than they fail don't they?
And let's face it, WHO among the viewers of Fox News, and the visitors to Breitbat's blog, were going to buy it anyhow?
The MUCH more important question in my mind is HOW did Breitbart get that e-mail?
I don't share my private e-mails with ANYBODY! At least on my end, the only two people who should have seen it are Joe and I. And really WHY would Joe send it to anybody else?
So is it possible that we now have an American case of News Corp phone hacking techniques being used by a well known contributor to Fox News? That is the question that I want to see answered!
Tuesday, July 19, 2011
Rachel Maddow reveals that phone and computer hacking just business as usual for companies owned by Rupert Murdoch.
Visit msnbc.com for breaking news, world news, and news about the economy
Labels:
America,
computer hacking,
FOX News,
MSNBC,
News Corp,
phone hacking,
Rachel Maddow,
Rupert Murdoch
Subscribe to:
Posts (Atom)